Can VDI Secure BYOD?
In 2006, Joanna Rutkowska stepped on stage at the Black Hat Conference and demonstrated a hack she called the “Blue Pill.” The name, of course, was in reference to the Matrix, because this attack made it almost impossible for victims to realize that they were trapped in a false virtual world–or in this case, a false virtual desktop.

Rutkowska’s attack worked by taking control of Windows Vista hypervisors, which let her command the server’s entire VDI ecosystem and access the data it protected. Still, this was just a demonstration. It wouldn’t be until 2022 that bad actors managed to pull off a “hyperjacking” attack in real life and show exactly how devastating it can be.
In the years since this demonstration, virtual desktop infrastructure (VDIs) have become popular tools,
and are often recommended for large enterprises managing BYOD scenarios.
But, just like the virtual world of The Matrix, they are not free from vulnerabilities
and require human batteries to function come with significant operational costs.
VDI can solve problems for some teams, while for others, it creates unmanageable technical complexity. Let’s figure out which camp you fall in.
What Is VDI?
VDI is a technology that lets end-users access remote desktops on their devices. To the employee, using VDI feels like a desktop and all its applications are running on their machine, but it’s all hosted on a distant server that potentially provides virtual desktops to many machines.
VDI has been around since the mid 2000s, but it saw a sharp uptick during the COVID-19 pandemic. When stay-at-home orders hit, companies had very little time to shift to a remote workforce and employees were abruptly stuck at home, often with no way to work except on their personal devices. VDI appeared as an option to let all of those varied endpoints access company systems remotely and securely.
Even without a global pandemic, this is how VDI tends to be used: to manage distributed workforces and as an alternative to other forms of device management.
There are a lot of VDI options out there–Citrix, Microsoft, and VMware are a few of the major players. They have various differences in terms of things like privacy policies and software requirements, but we’re not going to delve into those specifics in detail. Instead, consider this a broad overview of how VDI works.
As an example: we mentioned that VDI is mainly used by larger enterprises. That doesn’t mean that there aren’t any VDI options looking to serve smaller businesses. But it’s fair to say that broadly speaking, VDI is much better suited to large enterprises who can afford to host and maintain its complex infrastructure.
How VDI works
VDI works in three stages:
Data is hosted on physical servers in a data center.
On top of the physical server is a hypervisor. The hypervisor is a software layer that cuts up the server’s hardware capacity, then allocates and virtualizes those physical resources into separate virtual desktops.
Once a user installs the virtual machine software, they can open the remote simulated computer just like any other application on their device. The OS feels like a typical Windows or Linux desktop, but it’s being run and managed on the server and is sandboxed from all other applications on the host device.
These two terms are sometimes used interchangeably. But the essential difference between VDI and DaaS (desktop as a service) is that VDI, by definition, requires that “the business itself owns and operates the VDI servers.” With DaaS, you use servers owned and rented out by the DaaS provider. There’s plenty of overlap in how they work, but for the purpose of this article, we’re focusing on VDI and its various bugaboos.
Persistent vs non-persistent virtual desktops
Virtual desktops come in two flavors, with marked differences to security and user experience:
Persistent VDI: a user has one virtual desktop assigned to them. They can save changes, download software, and customize it to their needs. It works like an apartment. The company owns it, but the user chooses the furniture.
Non-persistent VDI: a user is assigned a temporary virtual desktop every time they log in. When they log out, everything is reset to the “golden image,” or the default desktop designed by their company. It works like a hotel room. Workers check in and use whatever’s there. When they leave, anything left behind gets wiped down and remade back to the uniform standard.
Non-persistent VDI makes the most sense for employees like call-center workers who just need to log in, use certain pre-selected apps, and then leave. It’s also commonly considered more secure, since the desktop and files get rebooted and wiped clean after every session.
The Benefits of VDI
For large enterprises that can afford the maintenance and IT costs, VDI can be a viable and even cost-saving technology. When rolled out at scale, and to workers who can tolerate its limitations, VDI offers security and compliance benefits.
Data governance
With so many people working from home, data leakage has become a more pressing concern. Employees might print out sensitive files (a particular concern in healthcare and law) or download sensitive data to endpoints that are vulnerable to theft, malware, or Shadow IT. Keeping data on remote servers, far away from the endpoint, helps protect it from bad actors or general data leakage. As Erica Mixon puts it for TechTarget, “A thief who steals a laptop from a VDI user can’t take any data from the endpoint device because no data is stored on it.”
VDI also lets IT teams exert a lot of control over user behaviors, and these capabilities can be customized pretty thoroughly through a lot of granular policies. For instance, IT can stop certain users–depending on role or need–from downloading records onto their physical computer, printing, copy-pasting from the virtual desktop, or using USB devices at all. Teams could even go so far as to encrypt any data that passes across the network, including by layering it with a VPN.
However, none of these features are foolproof, and none of them come without tradeoffs. Malicious insiders can still find workarounds for some of these safeguards (like taking photos of their computer screen). These features can also harm productivity and employee morale, since losing the ability to copy-paste has a significant impact on usability and is likely to make workers feel like they’re under suspicion.
Still, security requires friction, and VDI may create the friction that your team needs to protect sensitive data.
Regulatory compliance
Sectors like higher education, finance, and healthcare all have strict regulations around keeping client data safe. VDI can help prove compliance with those standards, so organizations can pass internal and external audits.
For instance, IT consultants IP Pathways published a case study describing their rollout of VDI at Brodstone Memorial Hospital. The small hospital wanted a way to access electronic patient records across different facilities. However, “Because of the stringent requirements of HIPAA HITECH, disaster recovery and continuity of patient records was imperative.” In this case, VDI suited their needs and provided an “attestable” way of proving that they were meeting the various requirements around sensitive patient records. Other case studies show VDI being used to let “clinicians use BYOD” to provide virtual healthcare while maintaining HIPAA compliance.
Device flexibility
In fact, if your company needs to maintain compliance on a variety of devices, VDI is a very flexible option.
With VDI, the server hosts almost all of the processing for each employee’s desktop. While those servers need to be powerful, not that much actual computing happens on the endpoint itself. This means that you can run a cutting-edge OS on a device that would normally not be powerful enough to support it. (Think of it as putting a Ferrari engine in a Toyota Corolla.) It also means that companies can keep older devices in circulation longer, instead of paying to upgrade them every few years.
With VDI, companies can have employees use older or lower-spec devices–like Chromebooks–without as much cost to usability. That cost-effective Chromebook is essentially just serving as a monitor and keyboard to interface with a much more powerful virtual machine.
Companies can also install VDI on specialized endpoints like zero clients (which have no OS of their own, just enough firmware to access the server) or thin clients (which have a very limited OS). These are devices that are basically only designed to access the server. To give an idea–the average Chromebook has historically been considered too powerful to count as a true thin client.
Both of these options are cheap, or even free if you convert your company’s older computers into thin clients. That reduces costs and e-waste, which is definitely a plus.
Companies can also use “thick clients,” or…regular computers (or tablets or phones) to access the virtual desktop. The point is, VDI is basically device-agnostic, and that’s one reason that it’s so often recommended for managing contractor devices or other common BYOD scenarios where traditional device management tools like MDM won’t work.
User privacy
BYOD security often comes up against the issue of employee and contractor privacy. Employees wonder if the data on their personal devices is safe from their company’s monitoring, and often resist IT’s attempts to manage those devices via MDM and other tools.
VDI isn’t the worst option on that front. It doesn’t have to be invasive because, in theory, it doesn’t ever interact with the data on a device. The only data accessed is the data needed for the employee to do their job–all of which is hosted on the virtual desktop.
Certainly there are options that give managers more visibility into user activity. But generally speaking, the monitoring VDI does is more geared toward diagnostics and monitoring network issues.
Overall, of the options available for use on personal devices, VDI is fairly non-invasive. But VDI still brings its share of usability issues.
The Drawbacks of VDI
Plenty of companies would love a solution that enables BYOD, solves their compliance headaches, and keeps their data secure. But there are good reasons VDI hasn’t caught on outside large enterprises. It’s not a particularly realistic option if you don’t have a lot of resources to support it. And even if you do have the budget and the IT staff to roll out VDI, the juice still may not be worth the squeeze.
There’s no Apple VDI
As a rule, VDI comes in two flavors: Windows or Linux. Apple’s licensing agreement forbids using or hosting MacOS “virtualized copies” for the purpose of “terminal sharing” or similar uses. Virtualized Macs exist, but the structure and scale of that virtualization operates differently than VDI and is usually intended for MacOS developers.
This might not be an issue if your workforce is already on Windows, but if you try and roll out VDI on knowledge workers who prefer Mac, there’s going to be a fair amount of frustration. Anyone who’s ever switched OSes knows that there’s a learning curve, and you’ll have to expect a productivity dip from users who keep forgetting where the downloads folder is.
And of course, for users who need access to Apple-specific software–like Final Cut Pro for film editing–you’ll have a bigger issue.
Speed/device performance
VDI requires that users access a desktop that’s hosted somewhere else. That creates some unavoidable issues, for the same reason that sending a letter across the country is more complicated than handing one to your roommate.
There are ways to mitigate VDI’s latency problems, but as David Linthicum reported for Infoworld, “…even if you pay for the faster stuff, a few days of detailed monitoring will show that latency and speed are pretty bursty overall.”
On top of that, the way VDI works means that multiple employees are sharing the resources of one server. Companies obviously want to get the maximum sustainable number of virtual machines out of each server, but finding that number is pretty complicated.
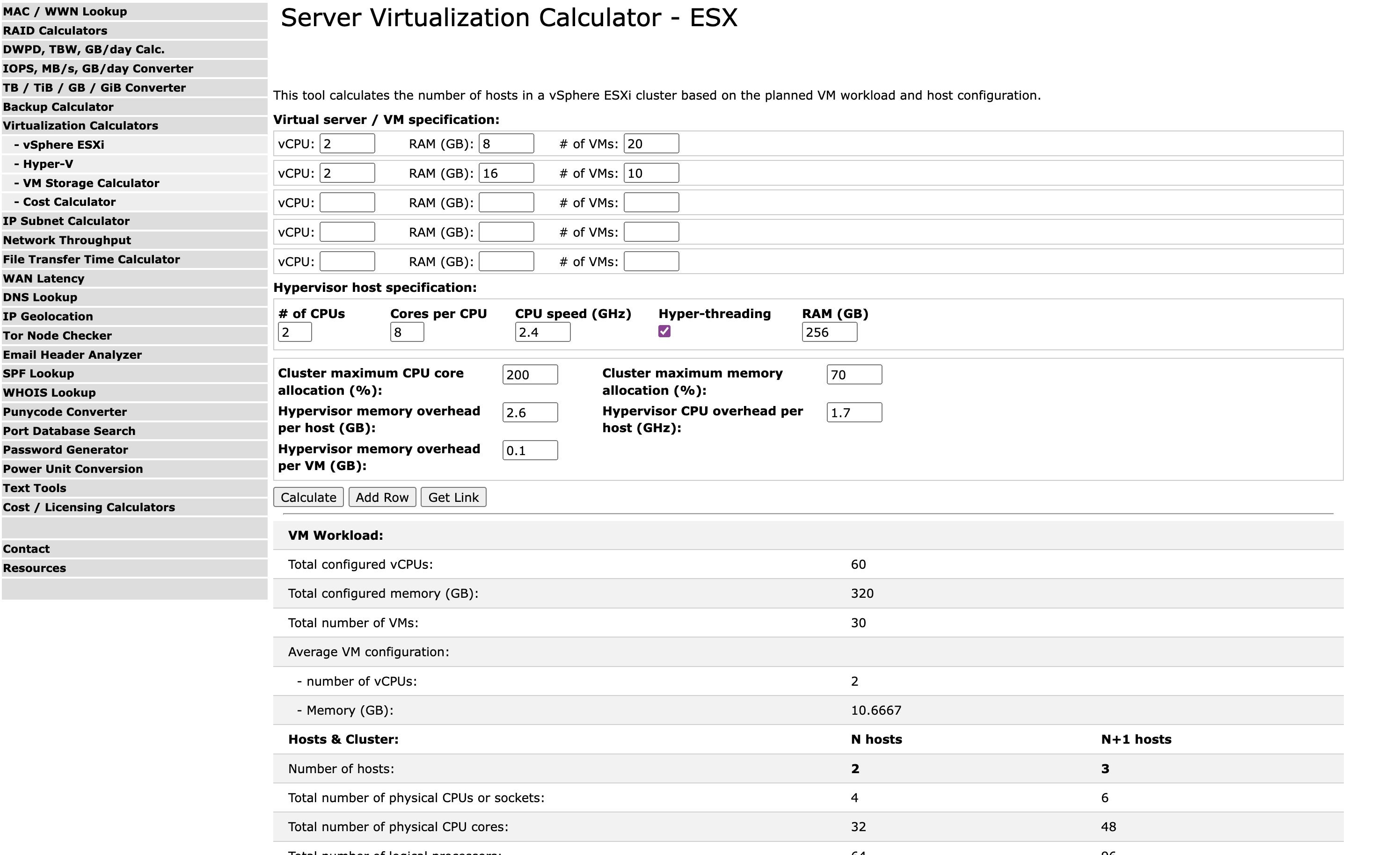
It’s very easy for IT to overprovision a server and promise too much of its power to too many devices (especially when the CFO is pushing them to err on the side of “lots”).
We previously established VDI’s use in healthcare, where urgency and security often conflict. Other case studies indicate the problems that VDI can cause in that kind of setting. One from Dell mentions that “VDI latency issues were decreasing productivity and threatening to impact care levels.”
Finally, just in case it doesn’t go without saying, VDI as a rule won’t work at all without an internet connection. That might not be a dealbreaker for some employees, who already rely on the internet to do their jobs. But it’s worth considering whether you can afford work grinding to a halt every time there’s an internet outage.
Deployment and maintenance expenses
Perhaps the biggest hurdle of VDI is that it’s expensive.
For starters, buying, housing, and maintaining servers represents a lot of cost. IT services vendor Intelligent Technical Solutions reported that, “a server that 20-25 people will use will cost around $15,000-$20,000 per server.” Depending on company size and the number of employees you need to cover, the costs of running a large enough data center can get into the millions pretty quickly.
Still, that’s far from the only cost of VDI. As Robert Sheldon put it for TechTarget, “The total cost of software can be one of the most expensive parts of implementing VDI. At the top of the list is the VDI software itself.”
VDI licensing costs are hard to predict, and involve various et ceteras. To manage your server’s virtualization, you might need any number of licenses or management tools for your hypervisors. You might also need to pay for a Windows license to run their OS. It all varies, again, depending on what you’re doing with each machine, like whether you’re going to operate on a per-user or per-device.
A lot of VDI’s costs come down to the specific needs of your company, meaning it’s hard to get estimates ahead of time. But Tatiana S., writing for the SystemAdminsPro Blog, shared her figures from helping the Evaluator Group figure out their infrastructure needs.
Her estimate had VDI software costs for 5000 knowledge workers coming out to $2,061,430–easily the most expensive part of their rollout.
That blog is from 2020. In recent years, VDI hasn’t been immune to the price hikes and corporate squeezing that seem to be impacting every product in every industry. Since VMware was purchased by Broadcom in November of 2023, they’ve stopped selling or supporting perpetual licenses that they previously offered for many of their VDI management software tools. They now operate on an exclusively subscription model.
The Security Vulnerabilities of VDI
Overall, VDI has earned a reputation for security–and that reputation might be its biggest vulnerability. VMware themselves fully admit: “Although known for its intrinsic security capabilities, VDI can present unique security risks.” As specific points of vulnerability, they list: hypervisors, networks, employees, and unpatched virtual machines.
Vulnerable endpoints
There seems to be a misconception that if a device uses VDI, then you don’t have to worry about that device, since it’s isolated from your systems. But all of this software still connects, and bad actors can use those connections.
There’s a good reason that Microsoft recommends endpoint protection even for non-persistent VDI, saying “Like any other system in an IT environment, [VDI Devices] too should have an Endpoint Detection and Response (EDR) and Antivirus solution to protect against advanced threats and attacks.”
VMware explicitly recommends using endpoint protection as part of a Zero Trust model, saying, “Continuous verification of device and desktop state…can help determine and put into effect the level of access that a user should have in any given situation.”
Malware and unpatched vulnerabilities
An end user on VDI can still let malware onto a virtual machine, where it can lurk like a parasite and potentially move upstream into other systems.
Even malware downloaded to a non-persistent VDI might have time to move from the virtual desktop into company networks before everything gets wiped. Remote Access Trojans (RAT) are one example of how a device that’s already infected with malware can be used by bad actors to force infections into a company’s VDI system.
Similarly, unpatched devices (even thin clients) can still leave VDI and servers vulnerable. Tenable described one path in which the Log4Shell vulnerability could let an unpatched Linux device connect to Microsoft’s Active Directory and then “escalate its local privilege and move laterally to all Tier-1 machines.”
Hypervisor attacks
Hypervisors still haven’t ever been hacked as subtly as Joanna Rotkowska’s Blue Pill attack. But when the hypervisor gets attacked, things still get scary pretty quick. The 2022 hyperjacking attack let bad actors push files to companies’ hypervisors, controlling and accessing every virtual desktop on that server.
Ransomware gangs have also targeted hypervisors more and more in recent years. During the MGM hack, ALPHV claimed to have “encrypted more than 100 ESXi hypervisors.” Similar hypervisor ransomware attacks had compromised “more than 3200 servers” by February of 2023, locking companies out of vital systems.
These cases of compromised hypervisors tend to start with credential-based attacks. You can’t pull this off like this with any old employee credentials, of course, but if bad actors get the credentials of super-admins, they can use them to access a company’s hypervisors. As Mandiant consultant Alex Marvi put it, “…you can compromise one machine and from there have the ability to control virtual machines en masse…”
The hypervisor touches everything on your server, from virtual machines to private data. And that goes both ways–everything else leads back to the hypervisor. One superadmin’s compromised credentials can let bad actors work their way laterally across your systems. (The moral of this story is that your superadmins’ authentication factors should be airtight.)
VDI Isn’t Secure Enough to Secure BYOD (On Its Own)
Say you’re a beekeeper who’s deathly allergic to bees. You’re going to wear your beekeeper’s outfit when you visit the hives–but you’ll also still carry your epipen.
VDI’s reputation has a lot of companies treating it like an impenetrable force-field strong enough to let them neglect other forms of security.
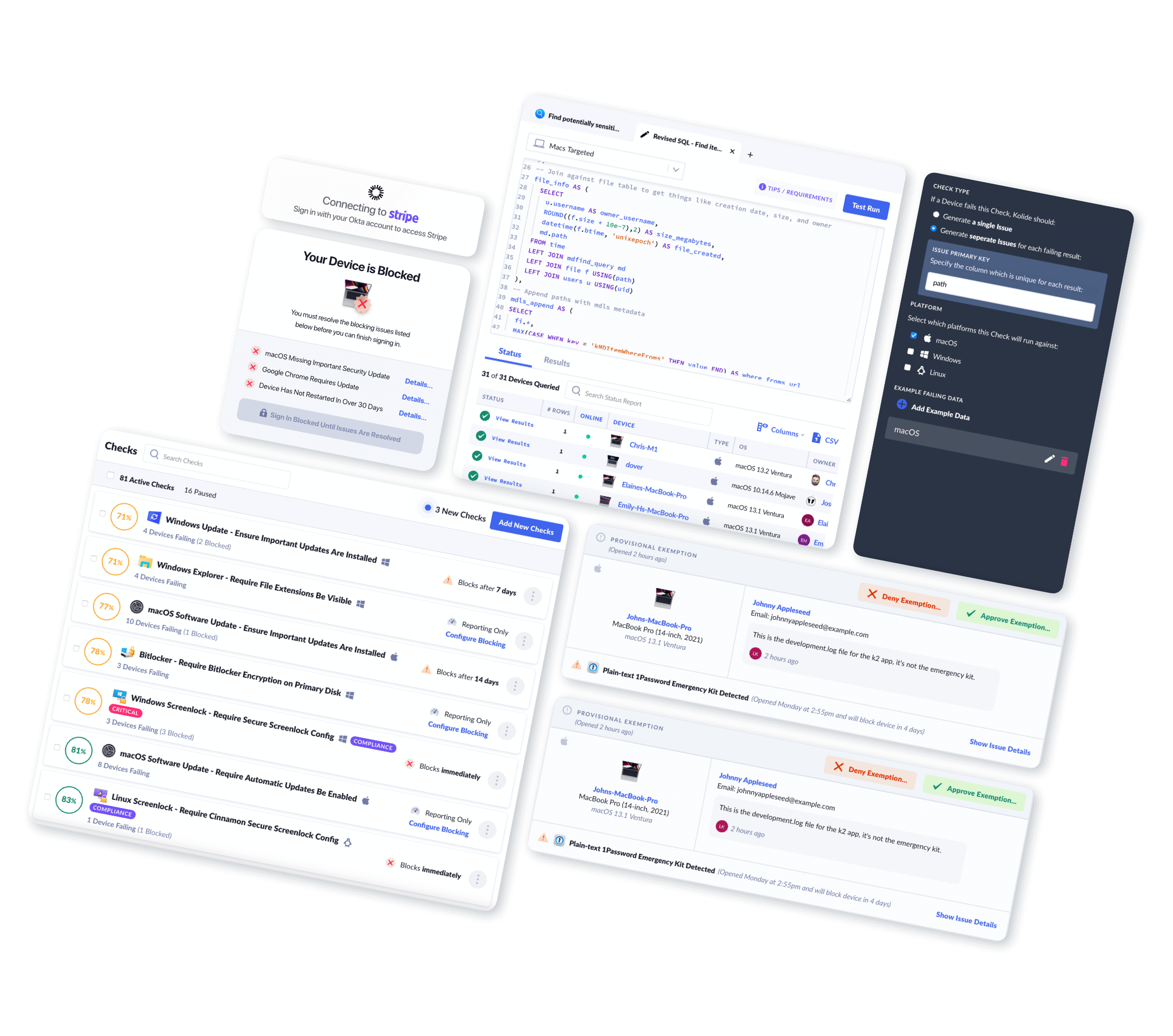
That’s despite the fact that the VDI companies themselves advise using their products with additional protections. VDI is still vulnerable, and the endpoint very much still matters. A lot of those vulnerabilities can be nullified if you make sure that only secured and verified devices can access your servers. (To see how Kolide does that, read more here.)
Even then, we won’t pretend that this is enough to make perfect security. And with VDI’s various complexities, it’s going to take a lot of work to figure out if it’s worth it for your company.
Want more original and curated stories about IT and security? Subscribe to the Kolide newsletter.