Do Macs Need Third-Party Antivirus for SOC 2 Compliance?
Osquery Makes the Built-In Security in macOS Audit Ready
Want to skip the preamble? Go right to the osquery SQL at the end of this article.
Third-party malware detection and prevention (what we used to call antivirus over a decade ago) is not every Mac Admins’ cup of tea. Some have bigger fish to fry (e.g., getting endpoint visibility, for starters); for others, they are content with the built-in anti-malware capabilities of macOS and thus have no plans to deploy AV on its merits.
Unfortunately, SOC 2 and other similar audits are forcing both types of Mac Admins to purchase and deploy antivirus-like software earlier and earlier in the organization’s lifecycle. When I ask IT Admins who weren’t psyched about deploying AV why they did it anyway, their responses generally fall into two buckets:
- They don’t believe macOS has sufficient anti-malware capabilities to pass a SOC2 audit.1
- They cannot pass compliance audits like SOC 2 without enterprise reporting features around malware protection (which Apple doesn’t have for its AV features)
In this article, we’ll challenge both of these assumptions. Most importantly, I want to show that with open-source tools, you can pass a SOC2 audit with the built-in anti-malware in macOS while also being able to defend that position to senior leadership and auditors. To do that, I hope you’ll indulge me in shoving the third-party AV industry around a bit in the process.
Holistically, macOS Built-In Security Is Better Than Third-Party Antivirus
Ideally, before you face a SOC 2 audit, you truly believe you’ve made the best decisions possible when it comes to the security of your Macs with the resources you have available. For example, as a security practitioner, I do actually believe that many organizations are better off relying on the built-in security capabilities of macOS without a third-party supplement. How can that be?
Well, for starters, let’s first acknowledge that the most basic and cursory research around third-party AV portends a horror show of tangible consequences that include: tanking an endpoint’s performance, regularly blocking legitimate software, indiscriminately selling users’ data to undisclosed parties, and even the software itself becoming the source of major compromise.
Okay, but not every vendor is equally afflicted by these problems so it’s not really fair to indict the entire of third-party AV industry on just those anecdotes.
So now, let’s talk about what we mean by “better.” In my view, the most myopic and flawed way to ascertain the quality of antivirus software is only to measure how good it is at stopping bad things from happening. These measurements include:
- How fast can the AV detect novel/new threats?
- How many real-time executions of bad things did the AV stop?
- How many novel areas of visibility can it obtain?
It’s no wonder that AV security companies build their entire pitch based on these measurements. Unfortunately, these measurements fail to consider the costs paid (usually by the end-user) for the marginal improvements across these metrics. Or put another way:
Kinda like how a lightbulb that sets things on fire is still high quality, so long as you only measure lumens?
— Tavis Ormandy (@taviso) November 19, 2016
The end-user misery generated by third-party AV is typically only addressed when it becomes so egregious that it can be easily linked to a significant adverse financial event. Misery is unbounded for everything that falls short of that bar. Accounting for this, we need to adjust how we accurately measure the AV’s actual performance.
Here is one way. Instead of just looking for the best antivirus performance at any cost, we need antivirus performance per unit of yuck, where yuck is defined as the qualitative degradation of the device’s user experience.
So who is better incentivized to give us maximum AV performance per yuck? In my view, it’s clearly OS vendors (like Apple), and here are the reasons why:
OS vendors are financially impacted if users think their OS runs like junk. Third-party AV vendors, on the other hand, are actually incentivized to portray the OS vendor as incompetent to position themselves as unique experts.
OS vendors rely on a thriving third-party ecosystem of useful and fun software to drive the adoption of the OS itself. That means they must care deeply about how OS security impacts the viability of software. Third-party AV does not have any incentive to care about the viability of other software until their customers notice (and then rectify it by just simply adding it to an allowlist).
OS vendors can use vertical integration to develop highly efficient security systems deep in the kernel of the OS itself and rely on the existence of sophisticated security hardware like a TPM. Third-party vendors simply cannot hook in at this deep level (safely), and they cannot successfully advocate for dedicated hardware within the device that makes their technology better.
Given the above realities, it’s easy to see why Apple has upped macOS’ built-in security capabilities considerably over the past few years.
XProtect
XProtect is macOS’ built-in antivirus technology. Under the hood, it scans executables (when first launched or when they change) against a list of signatures in a standard industry format called YARA. Here is an example of a YARA rule in the XProtect signature file:
rule EICAR
{
meta:
description = "OSX.eicar.com.i"
XProtect_rule = true
condition:
filesize <= 100000000 and hash.sha1(0, filesize) == "3395856ce81f2b7382dee72602f798b642f14140"
}
While this rule uses basic hash file matching (you can see more powerful examples in a repo Scott Knight regularly refreshes), YARA is a significant leg-up over traditional hash-only matching, which fails as soon as the malware author changes a single byte of code. This is very similar (if not identical) to how many classic AV vendors approach malware detection.
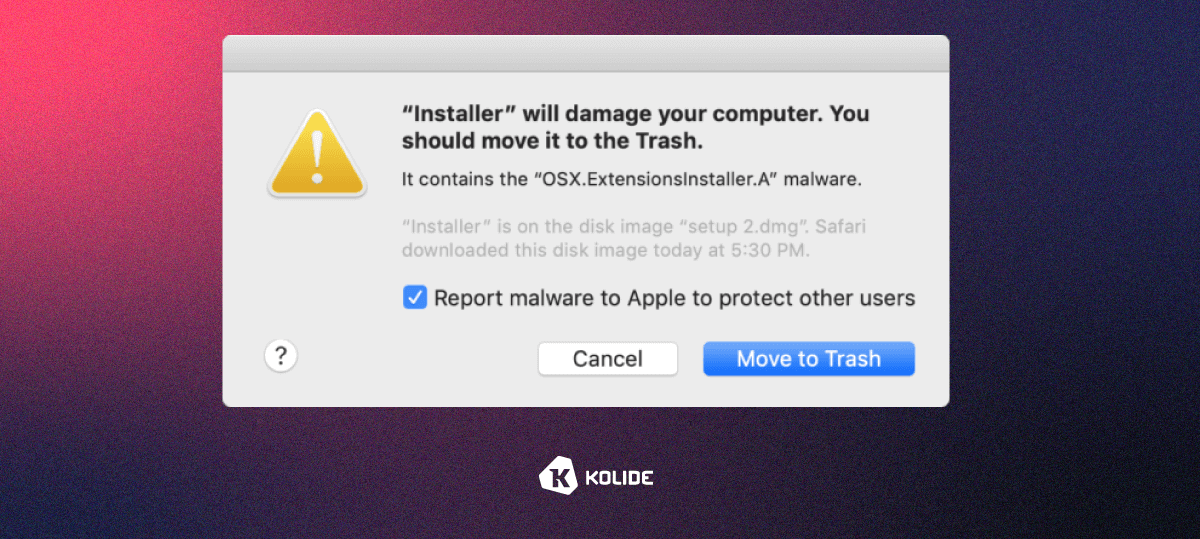
How these rules are put into practice is simple. When a file is scanned, if it matches any of the signatures, XProtect blocks the execution, generates logs, and finally alerts the user advising them to put the offending executable to the Trash.
Another great benefit is that XProtect updates itself automatically, silently, and separately from manually installed security updates. When these signatures are updated, XProtect will re-scan every subsequent app execution.
Malware removal tool
Even if XProtect fails to stop malware from launching, you’re not doomed. macOS’ Malware Removal Tool (MRT) remediates infections based on automated system data files and security updates from Apple and continues to check for viruses and malware anytime the user restarts or logs into the computer.
You may remember the MRT playing a significant role in the 2019 Zoom web server vulnerability. This is where Apple removed a vulnerable component of a third-party application using the MRT system.
Gatekeeper
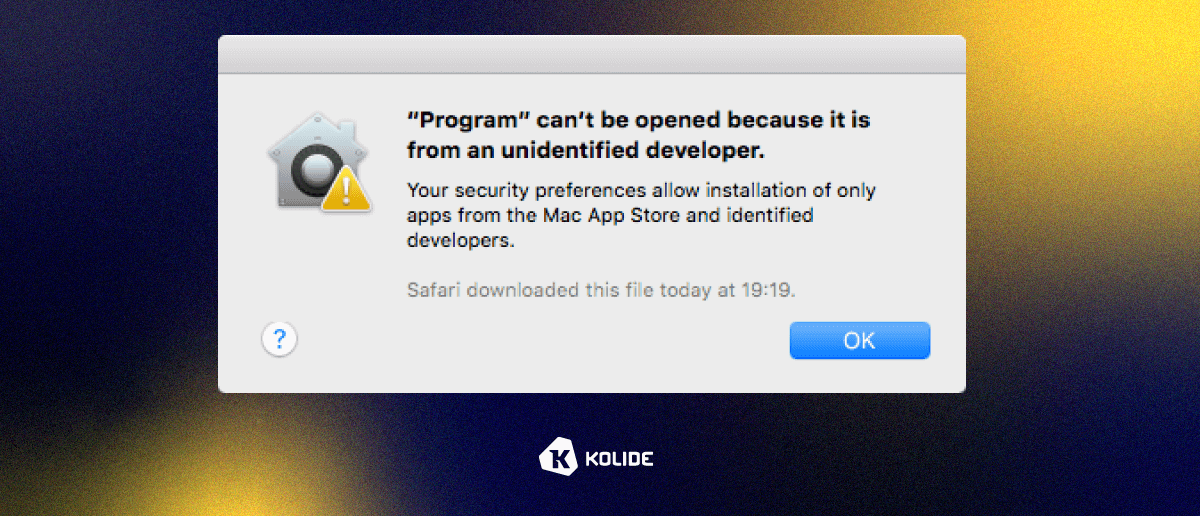
Gatekeeper is an integral part of the entire anti-malware apparatus on macOS. It plays a critical role in checking executables’ digital signatures to ensure they are coming from verified developers. This ensures that new executables that could be coming from unsafe sources (ex: downloading an app from a website) are handled to prevent them from harming the system until both the user and system can verify they are safe.
TCC permissions and System Integrity Protection
macOS 10.15 and above requires all apps to get users’ permission before logging their keystrokes or accessing files, camera, or microphone. Additionally, Apple stores macOS (Catalina and above) on a separate disk volume to separate essential system files from the applications. As long as System Integrity Protection is enabled, these files cannot be modified by any processes.
Other macOS security features
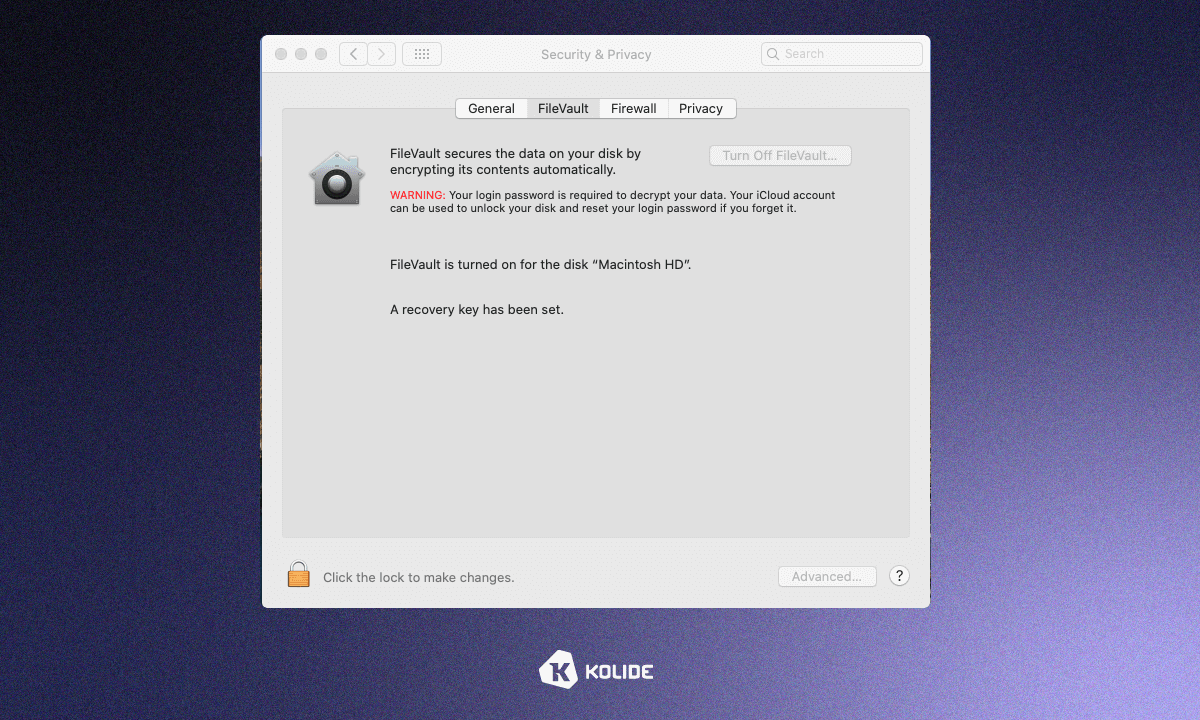
macOS offers improved password protection and two-factor TOTP support in Monterey (by way of the new Keychain). Apple added a recording indicator to let users know if an app records their activities through the mic. Meanwhile, FileVault can encrypt data stored on a Mac.
Additionally, Safari uses anti-phishing technology to detect fraudulent websites and prevent plug-ins such as Silverlight, QuickTime, and Oracle Java from running if they aren’t updated to the latest version.
Investing in Prevention Has Quickly Diminishing Returns. Instead, Focus on What You Will Do When That Prevention Eventually Fails
AV vendors’ common arguments to justify their products despite Apple’s comprehensive built-in security are all about splitting hairs around detection efficacy.
The playbook generally involves the third-party AV vendor pointing to specific malware variants that their product can detect and that Apple failed to add to their signature lists promptly (or at all).
In my view, this is a foolish argument to mount. It’s easy to enumerate many successful malware campaigns that no antivirus vendor could detect in a in a timely manner. Since perfect detection/prevention is not possible, we must consider the trust cost we wish to pay in terms of guaranteed performance degradation, false positives, and additional attack surface to get very marginal improvements. If users are keeping a tight ship, applying updates, and not disabling Gatekeeper, that strongly correlates with a very low chance that those differences in protection impact them.
Expanding upon the idea that prevention eventually fails, at some point, it makes sense to find a reasonable baseline of preventative antivirus and shift focus and resources into building a computer incident response plan. That means when (not if) a Mac does become compromised, the organization can better react to mitigate the potentially severe impacts of that compromise going unchecked. The prevention game is one with serious diminishing returns per dollar spent. On the other hand, incident response development is one of the best security investments you can make.
But There’s a Missing Piece: Compiling Data To Meet Audit Requirements
As we saw above, Apple is incentivized and does a reasonable job protecting Mac users from malware.
That’s great news! But there’s one problem.
You still need to collect data to compile reports for your compliance audit, and macOS doesn’t offer a way to achieve that level of fleet visibility.
That’s where osquery comes to the rescue.
You might have heard of using osquery to take device inventory, but did you know it’s also a handy tool for compiling data to meet SOC 2 reporting requirements?
How osquery supports SOC 2 compliance
Osquery is an open-source tool that allows users to query operating systems. For example, IT can use osquery to gain visibility into macOS, Windows, and Linux devices.
You can use osquery to check all the devices in your fleet. This allows you to ensure that they follow platform-specific rules based on your company’s data security policy and compliance standards (e.g., disk encryption, firewall status, OS updates, etc.)
Osquery can accumulate and log compliance data to support the SOC 2 reporting and the auditing process. You can see aggregated metrics or drill down to specifics using various filters to demonstrate that users’ devices are compliant with SOC 2 requirements.
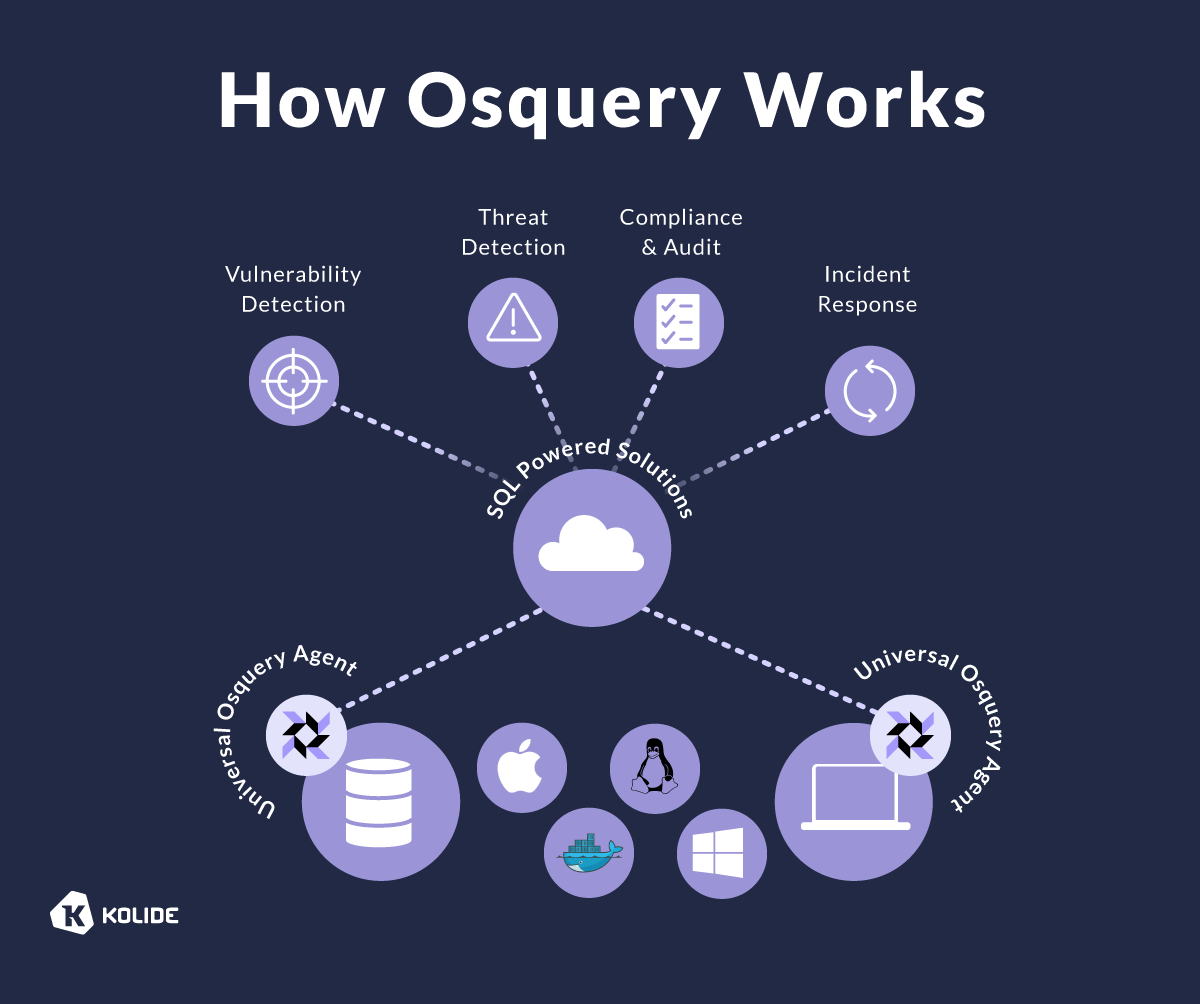
Many IT professionals favor osquery because it’s simple, reliable, and extensible. Since it works for all three operating systems, you can collect data on every device in your fleet without using different tools.
How To Use Data Collected By Osquery to Support SOC 2
To pass your SOC 2 audit, you must create documentation to demonstrate that your systems and processes meet specific requirements.
To show that you have the appropriate defense against malware and viruses according to Common Criteria 6.8, you must create a report to describe your processes for file integrity monitoring (FIM) and endpoint security management.
Your documentation should demonstrate that:
You can track updates made to software and configuration files and changes in endpoint protection statuses and events.
You have implemented controls to prevent, detect, and act upon unauthorized or malicious software introduced into your infrastructure.
Only authorized individuals can install applications and software on devices connected to your network.
You have processes to detect changes that could indicate the presence of unauthorized or malicious software.
There’s a management-defined change control process to monitor the implementation of software and applications.
Antivirus and anti-malware software is implemented and maintained to detect and remediate malware.
You follow procedures to scan information assets in your custody to detect malware and other unauthorized software.
Below is an example of the documentation we provide customers upon request to help them pass these criteria for their SOC 2 compliance with Kolide and macOS’ built-in protection.
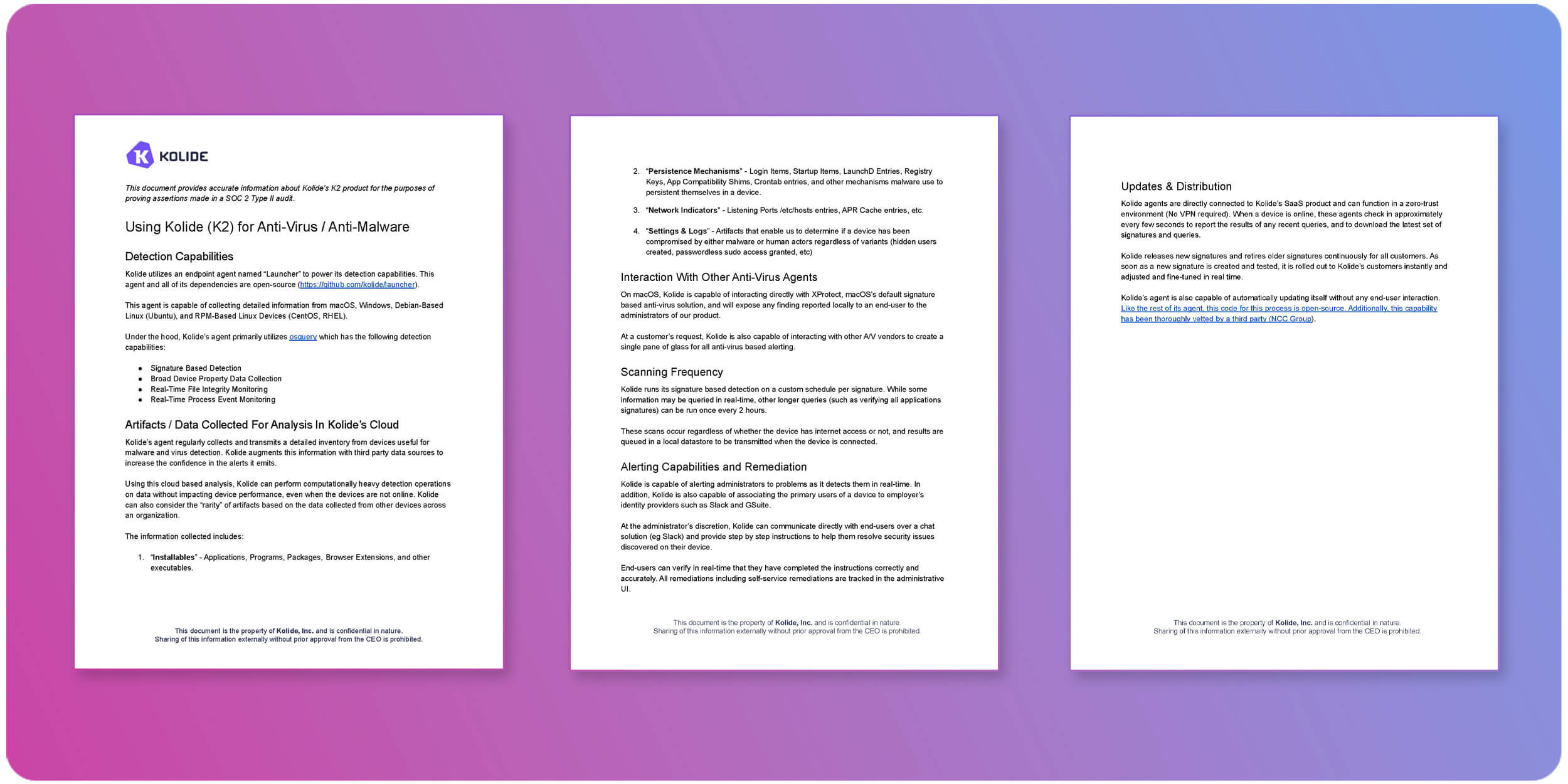
Putting osquery into action for SOC 2 compliance
macOS can satisfy the technical requirements for SOC 2 certification, and you don’t need to use third-party antivirus. But it’s challenging to compile device data and report at scale. This is where osquery comes in to provide fleet visibility, monitor activities, and compile the data you need to prove fleet compliance for SOC 2 audit and reporting.
To establish that the overall malware prevention apparatus of macOS is operational, XProtect (the primary component) requires that two things be present and functional for it to work correctly:
The first requirement is that Gatekeeper must be enabled for XProtect to run on recently downloaded executables (basically any file where the quarantine bit is set to “true”).
The second requirement is that System Integrity Protection (SIP) is enabled to ensure the anti-malware services and their definitions are not modified by a bad actor.
Below is a selection of simplified queries Kolide runs automatically using the osquery agent:
Osquery SQL: Is Gatekeeper enabled? What version is installed?
SELECT * FROM gatekeeper
+---------------------+----------------+---------+----------------+
| assessments_enabled | dev_id_enabled | version | opaque_version |
+---------------------+----------------+---------+----------------+
| 1 | 1 | 8.0 | 94 |
+---------------------+----------------+---------+----------------+
Osquery SQL: When was the last time XProtect signatures were updated?
SELECT date(mtime,'unixepoch') FROM file WHERE path='/Library/Apple/System/Library/CoreServices/XProtect.bundle/Contents/Resources/XProtect.plist';
+-------------------------+
| date(mtime,'unixepoch') |
+-------------------------+
| 2022-03-11 |
+-------------------------+
Osquery SQL: Has XProtect blocked the execution of known malware?
SELECT * FROM xprotect_reports;
+-----------------+-------------+------------+
| name | user_action | time |
+-----------------+-------------+------------+
| OSX.eicar.com.i | trash | 1650480090 |
+-----------------+-------------+------------+
Osquery SQL: Is MRT available? What version is installed?
WITH MRT_info AS (
SELECT * FROM plist WHERE path LIKE '/Library/Apple/System/Library/CoreServices/MRT.app/Contents/Info.plist'
)
SELECT
MAX(CASE WHEN path = '/Library/Apple/System/Library/CoreServices/MRT.app/Contents/Info.plist' THEN 'MRT.app' END) AS name,
MAX(CASE WHEN path = '/Library/Apple/System/Library/CoreServices/MRT.app/Contents/Info.plist' THEN '/Library/Apple/System/Library/CoreServices/MRT.app' END) AS path,
MAX(CASE WHEN key = 'CFBundleExecutable' THEN value END) AS bundle_executable,
MAX(CASE WHEN key = 'CFBundleIdentifier' THEN value END) AS bundle_identifier,
MAX(CASE WHEN key = 'CFBundleName' THEN value END) AS bundle_name,
MAX(CASE WHEN key = 'CFBundleShortVersionString' THEN value END) AS bundle_short_version,
MAX(CASE WHEN key = 'CFBundleVersion' THEN value END) AS bundle_version,
MAX(CASE WHEN key = 'CFBundlePackageType' THEN value END) AS bundle_package_type,
MAX(CASE WHEN key = 'LSEnvironment' THEN value END) AS environment,
MAX(CASE WHEN key = 'LSUIElement' THEN value END) AS element,
MAX(CASE WHEN key = 'DTCompiler' THEN value END) AS compiler,
MAX(CASE WHEN key = 'CFBundleDevelopmentRegion' THEN value END) AS development_region,
MAX(CASE WHEN key = 'CFBundleDisplayName' THEN value END) AS display_name,
MAX(CASE WHEN key = 'CFBundleGetInfoString' THEN value END) AS info_string,
MAX(CASE WHEN key = 'LSMinimumSystemVersion' THEN value END) AS minimum_system_version,
MAX(CASE WHEN key = 'LSApplicationCategoryType' THEN value END) AS category,
MAX(CASE WHEN key = 'NSAppleScriptEnabled' THEN value END) AS applescript_enabled,
MAX(CASE WHEN key = 'NSHumanReadableCopyright' THEN value END) AS copyright,
MAX(CASE WHEN key = '-- not_available' THEN value END) AS last_opened_time
FROM MRT_info GROUP BY path;
name = MRT.app
path = /Library/Apple/System/Library/CoreServices/MRT.app
bundle_executable = MRT
bundle_identifier = com.apple.MRT
bundle_name = MRT
bundle_short_version = 1.91
bundle_version = 1
bundle_package_type = APPL
environment =
element = 1
compiler = com.apple.compilers.llvm.clang.1_0
development_region = en
display_name =
info_string =
minimum_system_version = 10.10
category =
applescript_enabled =
copyright = Copyright © 2020 Apple, Inc. All rights reserved.
last_opened_time =
Osquery SQL: Is System Integrity Protection (SIP) turned on?
SELECT * FROM sip_config;
+----------------------------+---------+---------------+
| config_flag | enabled | enabled_nvram |
+----------------------------+---------+---------------+
| sip | 1 | 1 |
| allow_apple_internal | 0 | 0 |
| allow_device_configuration | 0 | 0 |
| allow_kernel_debugger | 0 | 0 |
| allow_task_for_pid | 0 | 0 |
| allow_unrestricted_dtrace | 0 | 0 |
| allow_unrestricted_fs | 0 | 0 |
| allow_unrestricted_nvram | 0 | 0 |
| allow_untrusted_kexts | 0 | 0 |
+----------------------------+---------+---------------+
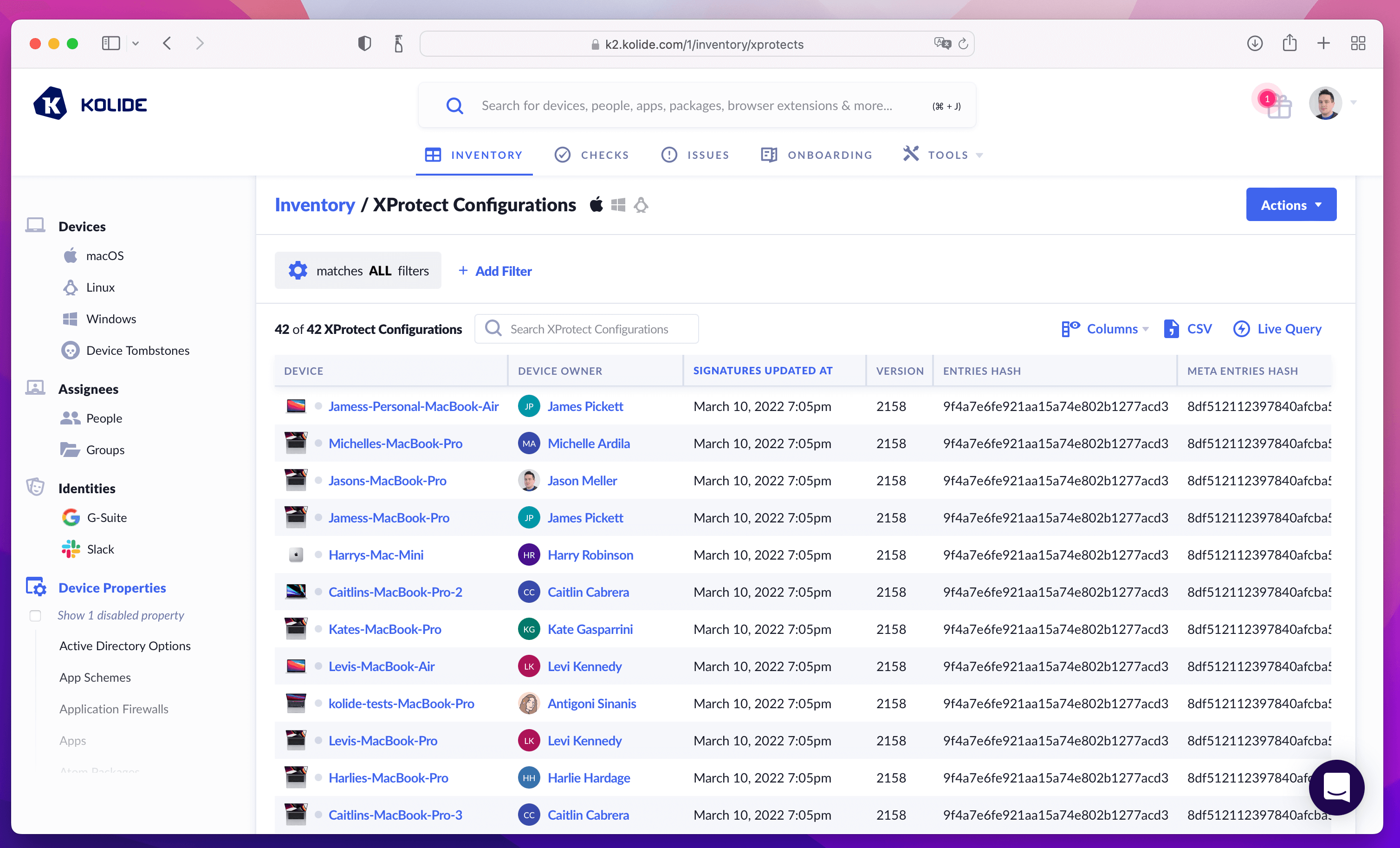
As you can see above, osquery can help collect important details about the state of macOS’ built-in malware and virus protection. The question now becomes, how do you best aggregate the data and show it to auditors?
Osquery out of the box emits logs that can be aggregated by third-party SIEMs and log aggregation tools. Using their native reporting functions, you can build a dashboard that will get you through your audit and give you incredible visibility.
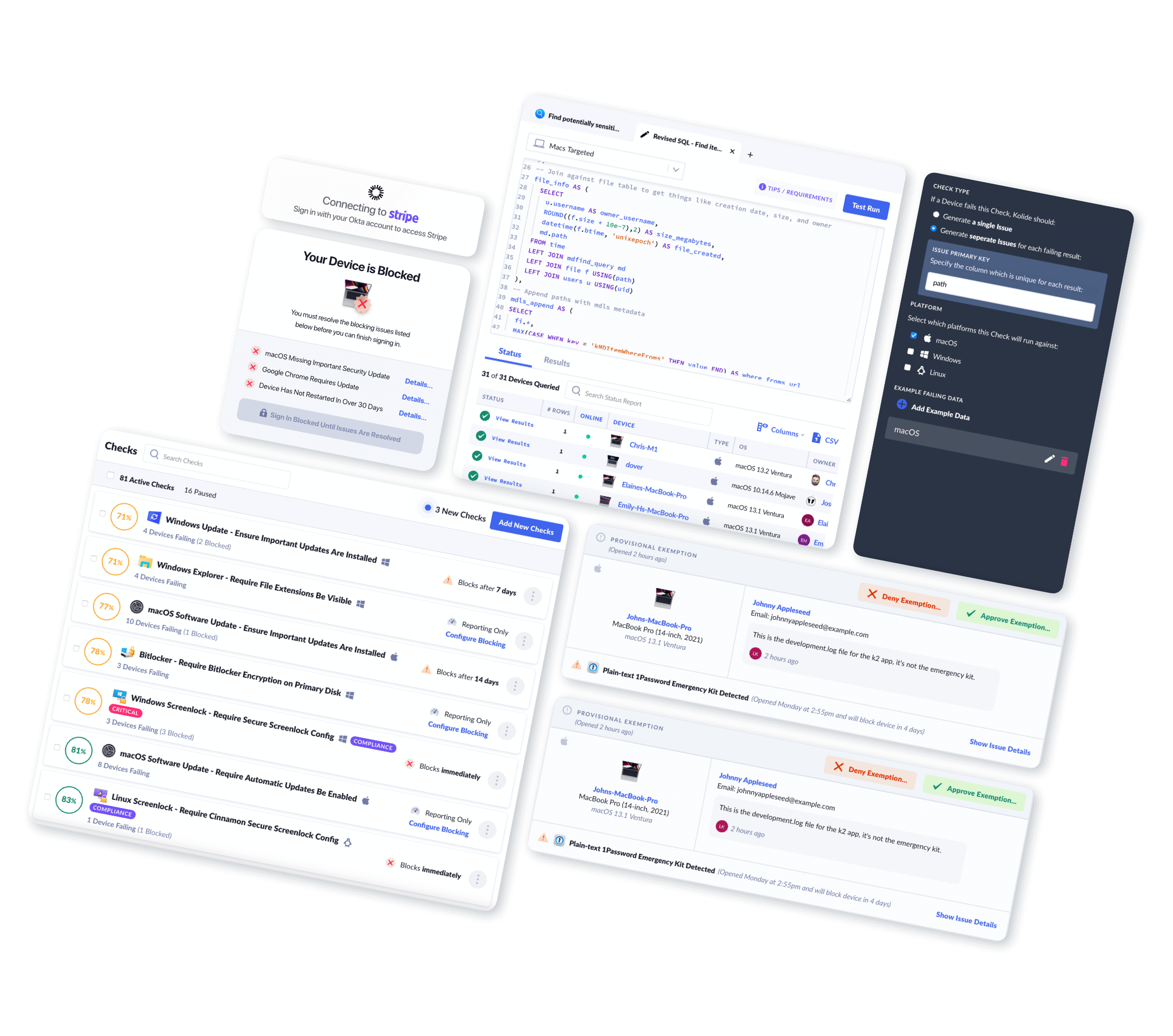
If you don’t want to build all this yourself, Kolide can get you up and running fast. Kolide’s product automatically gives you native installers for Macs, Windows, and Linux that install osquery. Once the agent runs, Kolide will automatically collect all the pertinent info, aggregate it, and visualize it. Within a few minutes, you could be looking at a dashboard like this:
Another question vanilla osquery doesn’t have an answer for is remediation. For example, if you find Gatekeeper or SIP is disabled, how do you fix them? One approach is to use an MDM to force something like Gatekeeper to be enabled. Unfortunately, other settings like SIP cannot be managed by these types of policies.
Again, Kolide can run checks against your Macs to verify that these services are enabled. If they aren’t, Kolide integrates with Slack to message end-users and directs them on how to re-enable those features (and explain why they are important to keep them that way).
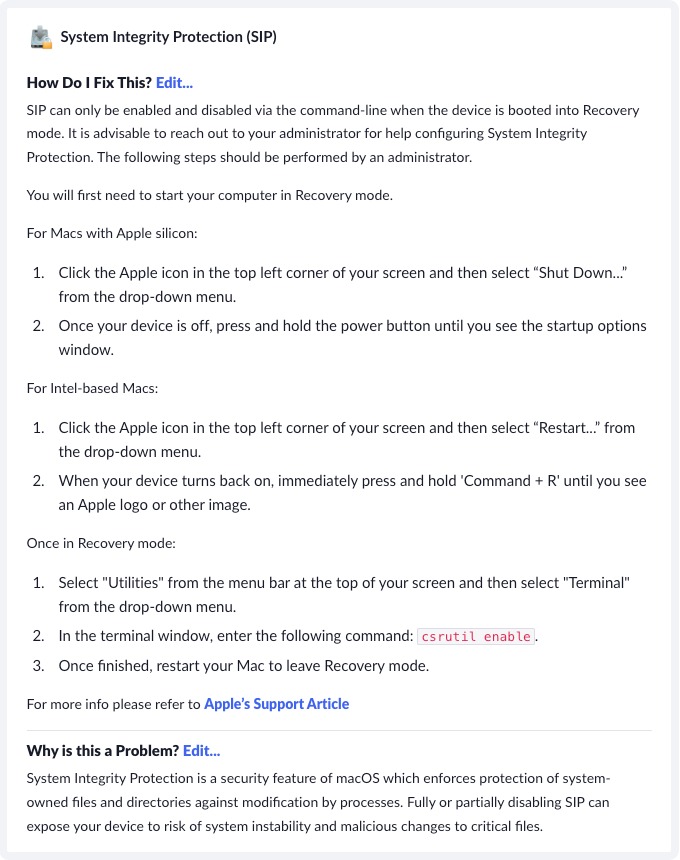
End-user notifications are a part of our Honest Security philosophy. We believe that teaching end-users how to keep their devices secure nets better and more complete security over simply locking the machine down.
To see how Kolide can secure your fleet and achieve 100% compliance, watch our on-demand demo today.
-
Compliance auditors get annoyed when you use binary terms like “pass” or “fail” to describe the outcome of an audit. Instead they use terms like “modified” or “qualified”. When I use the word “pass” in this article, I mean that you have obtained a SOC 2 report without negative qualifications. ↩