Managed vs Personal Apple IDs in the Workplace: an IT Guide
Apple devices rely on an Apple ID (formerly iCloud) account in order for various services and integrations to function (e.g., Find My), as well as to link software licenses purchased via the App Store. There are two distinct types of Apple IDs which a device may be configured/associated with:
- Personal Apple ID (default).
- Managed Apple ID (configured through Apple Business Manager).

Increasingly, employees are taking their organization-owned devices (such as MacBooks) off-site to use in a Work From Home context. This shift has resulted in a greater overlap of personal and work-related activity taking place on organization-owned devices. For this reason, many organizations are reevaluating whether to permit employees to use their personal Apple IDs. Here, we’ll go over the various options for end user Apple IDs and the tradeoffs associated with each.
Dealing with Apple ID in a Corporate Environment
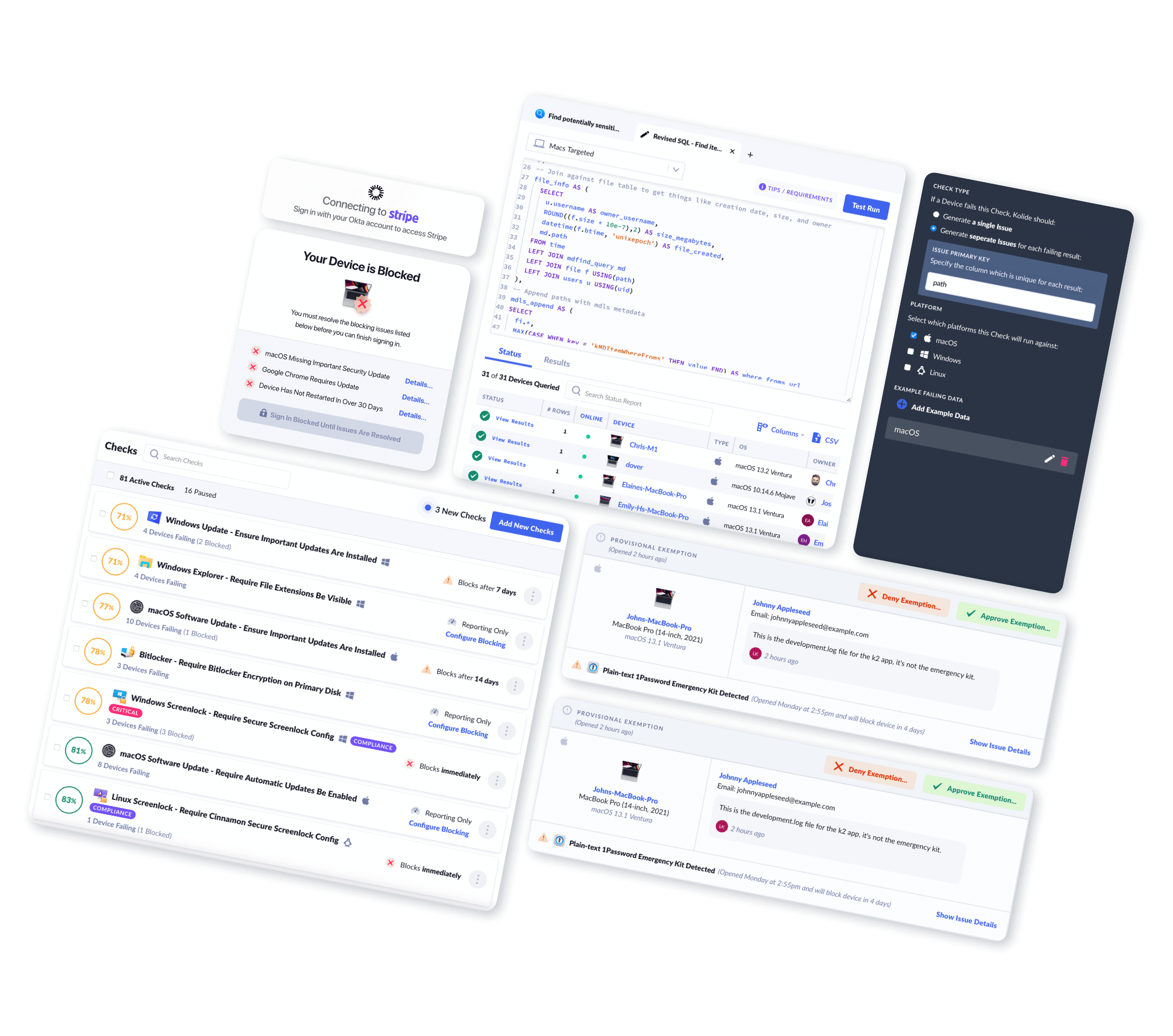
At Kolide, we are often asked to build Checks relating to the configured Apple ID on devices. The most common form this question takes is:
“I want to find individuals using a personal email address for their Apple ID account.”
Typically, admins want to forbid the use of personal Apple IDs in order to exercise greater control over their Apple devices. However, this task comes with a number of downstream effects which you should be aware of before deciding how to proceed.
Before we dive into the request, let’s unpack Apple ID for a moment. As mentioned above, Apple ID is a tightly integrated component of the macOS experience and understanding how it is used can help inform the scope of your security objectives.
What Capabilities Does Apple ID Enable?
The syncing services provided via a personal Apple ID are considerable due to the intended Quality of Life benefits they offer a normal home user:
Keychain: Includes password manager features which allow a user to securely generate and store authentication credentials.
Cloud Drive (Documents, Desktop, Photos): These synced User home directory folders allow a user to access documents they have saved via the Cloud.
Find My: Allows a user to remotely locate a device in the event it becomes lost or stolen.
Calendar, Contacts, and Mail: These basic apps/services can be configured with both personal and work information.
Media & Purchases: Apps purchased through the App Store are associated with the Apple ID which purchased them, and can be transferred from device to device.
Why Are Personal Apple IDs Sometimes a Concern for IT and Security Administrators?
There are a variety of reasons an IT or Security administrator may wish to limit or prohibit the usage of personal Apple IDs on company-provided devices. The following are some (but not all) possible reasons:

Shadow IT
Shadow IT describes personal or unmanaged applications or devices which are not within the purview of the IT or Security team at an organization.
A good example of Shadow IT would be an employee connecting their personal Dropbox account to their company laptop. An employer may worry that this personal Dropbox account could unintentionally sync proprietary or sensitive organization data, with no ability for the company to know what was synced or to revoke access in the event the employee leaves the company.
Activation Lock
Devices which have Secure Enclaves (T1 and T2 equipped Intel Macs, and all Apple Silicon Macs) and are not enrolled in MDM have a feature called Activation Lock. This feature works with Find My to prevent a device from being recovered or reimaged without the express authorization of the registered Apple ID on the device. This can pose an issue if a company-owned device (with Find My enabled) is returned to an IT department as the device will not be serviceable until that Apple ID has been disconnected or Find My has been disabled.
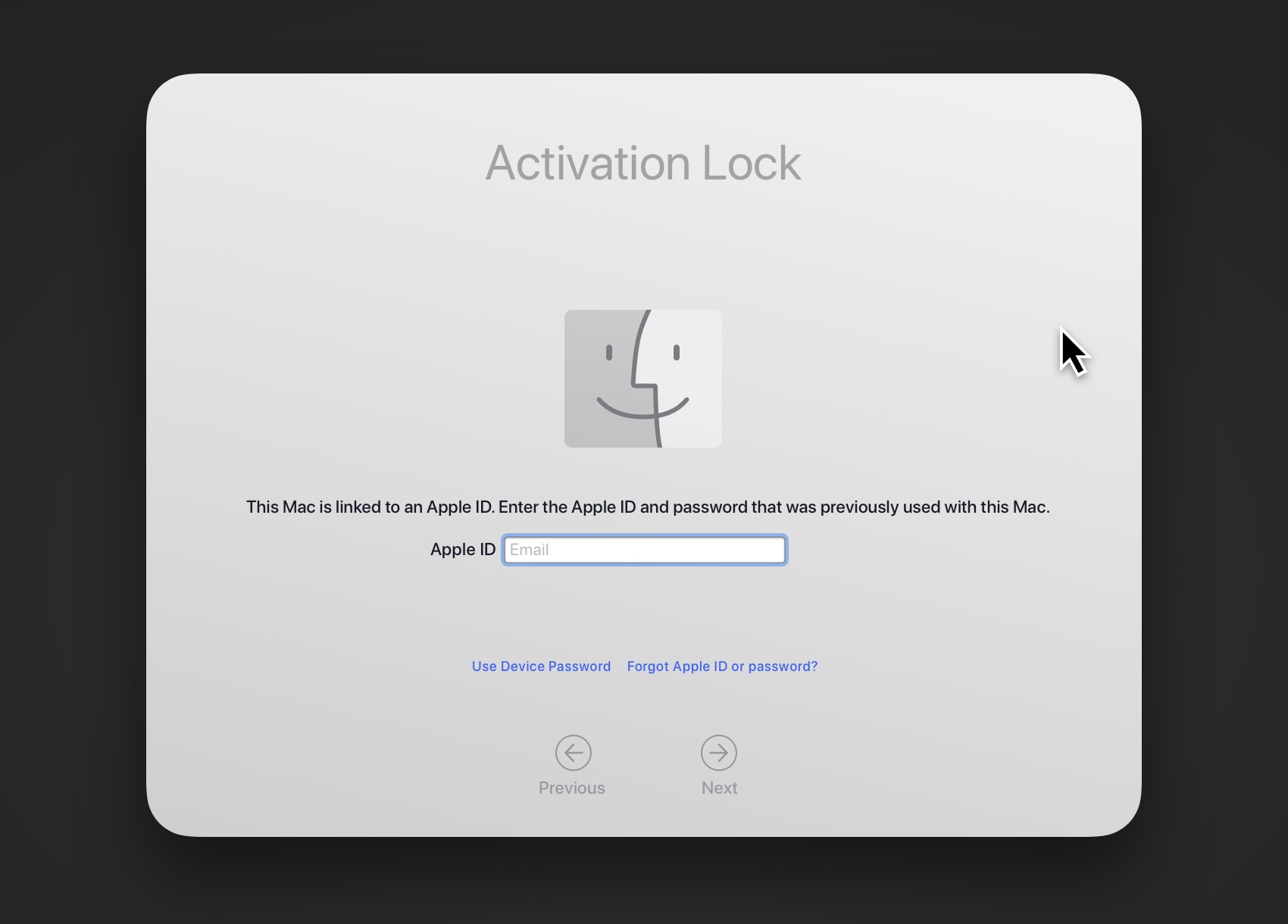
For this reason, Apple expressly recommends that personal users turn off Activation Lock when sending a device in for service or transferring ownership to another individual.
Software Provisioning
When an end-user purchases software licenses through the Apple App Store using their personal Apple ID, the license is non-transferable and linked to their Apple ID. This means that if the software is intended to be used for work purposes, that license cannot be re-provisioned to another end-user if the existing end-user discontinues their employment.
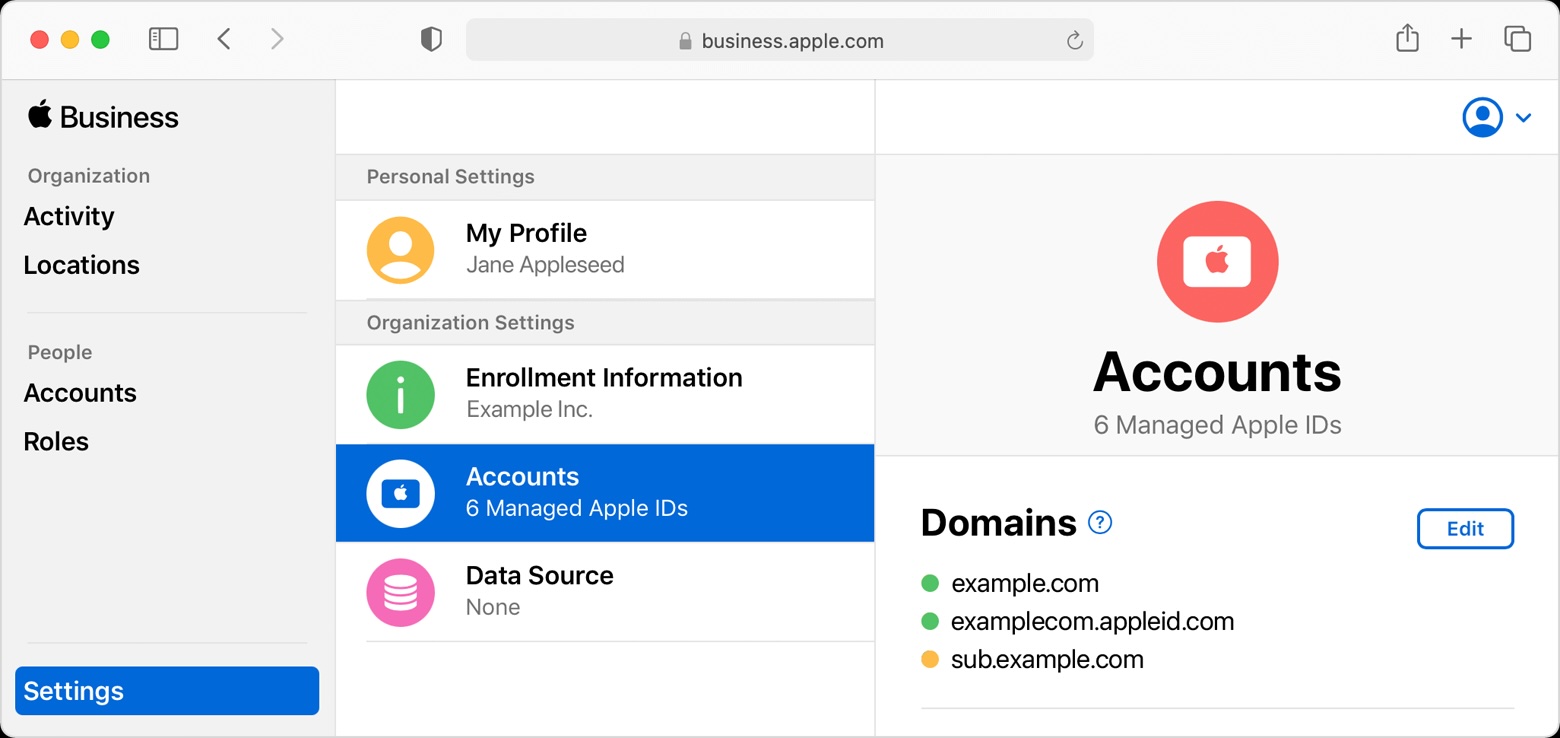
Managed Apple IDs: An Alternative with Restrictions
For a number of years, Apple has provided a more restricted version of Apple ID used in education environments called Managed Apple IDs. In 2018, these Managed Apple IDs were made available for Apple Business Program accounts as well. Managed Apple IDs are provisioned, configured, and managed through the Apple Business Manager portal.
Managed Apple ID Restrictions
While Managed Apple IDs are the only real alternative to personal IDs, they come with some real changes to user experience.
iCloud restrictions
- Find My is disabled.
- Health is disabled.
- iCloud Family Sharing is disabled.
- iCloud Mail is disabled.
- All iCloud+ services (e.g., Private Relay) are unavailable.
- Apple Pay is unavailable.
Media & Content restrictions
Apple’s media related services, subscriptions, and stores (e.g., Apple One, Apple Arcade, Apple TV+) are completely inaccessible with a Managed Apple ID.
In addition, users can browse but not purchase or download items in the App Store, iTunes Store, and Apple Books.
Instead, administrators must manually distribute apps through a Mobile Device Management (MDM) solution.
Managed Apple ID Benefits
- Apple ID access can be provisioned, configured, managed, and revoked for onboarding/off-boarding purposes.
- Apple ID passwords can be reset by an administrator if a user forgets their password.
- App Store app licenses can be centrally managed, purchased, and distributed/re-provisioned as needed.
- If iCloud FileVault recovery is configured, an administrator can recover FileVault without an escrowed key via Apple ID password reset.
As you can see, there are a significant number of considerations to take into account before deciding which path is best for your organization, and the level of control/restriction you wish to deploy.
What Are My Choices as an Employer?
Option 1: Allow end-users to use their personal Apple ID with their work laptop.
We believe this is the best choice for organizations that do not have an explicit compliance requirement prohibiting Apple ID/iCloud usage. The risk of unauthorized data syncing is no greater than an employee uploading or emailing sensitive files via other services. If your organization uses an MDM, you can manage items such as Activation Lock and FileVault2 Recovery without the need for a Managed Apple ID.
Option 2: Configure Managed Apple IDs for employees and require their usage.
This will permit greater control at the cost of reduced/restricted end-user functionality.
Option 3: Use a personal Apple ID with a corporate email.
See below for why this is not recommended.
Why not to use Personal Apple IDs with Company Emails
Having an employee use their work email to sign up for a personal Apple ID might seem like an ideal workaround, but in reality, you get none of the benefits of a Managed Apple ID, while negatively impacting the user experience of your employee (e.g., preventing them from installing app from the App Store).
You will not be able to:
- Centrally configure or manage company Apple IDs.
- Provision software.
- Reset passwords.
- Revoke access to AppleID services or synced data when the employee leaves.
Furthermore, the employee will still be able to sync files and services to iCloud, purchase software licenses, Activation Lock their device, etc.
A Caveat to these Limitations
Some teams work around the limitations of Personal Apple IDs configured via work email address by assuming they can access the employee’s email upon termination.
By accessing an employee’s work email (which they signed up for Apple ID with), an administrator may be able to reset the Apple ID password and delete any synced information, prevent the end-user from accessing that Apple ID, as well as ensure that any linked services requiring Apple ID authorization (e.g., Activation Lock) can be disabled by the administrator.
However…
Final Thoughts: Choosing the Right Apple ID Strategy
As we mentioned, we personally prefer letting employees use their personal Apple IDs, since it’s the option that gives them the most agency over their devices. However, there is no perfect option here, and every route requires some tradeoffs between security, privacy, and user experience.
It is ultimately up to the IT or Security team to decide which path is best for their organization. Kolide can then assist in identifying any Apple IDs connected to a device and emit notifications if they do not match the criteria you choose.