How to List SIP Settings Across All Macs
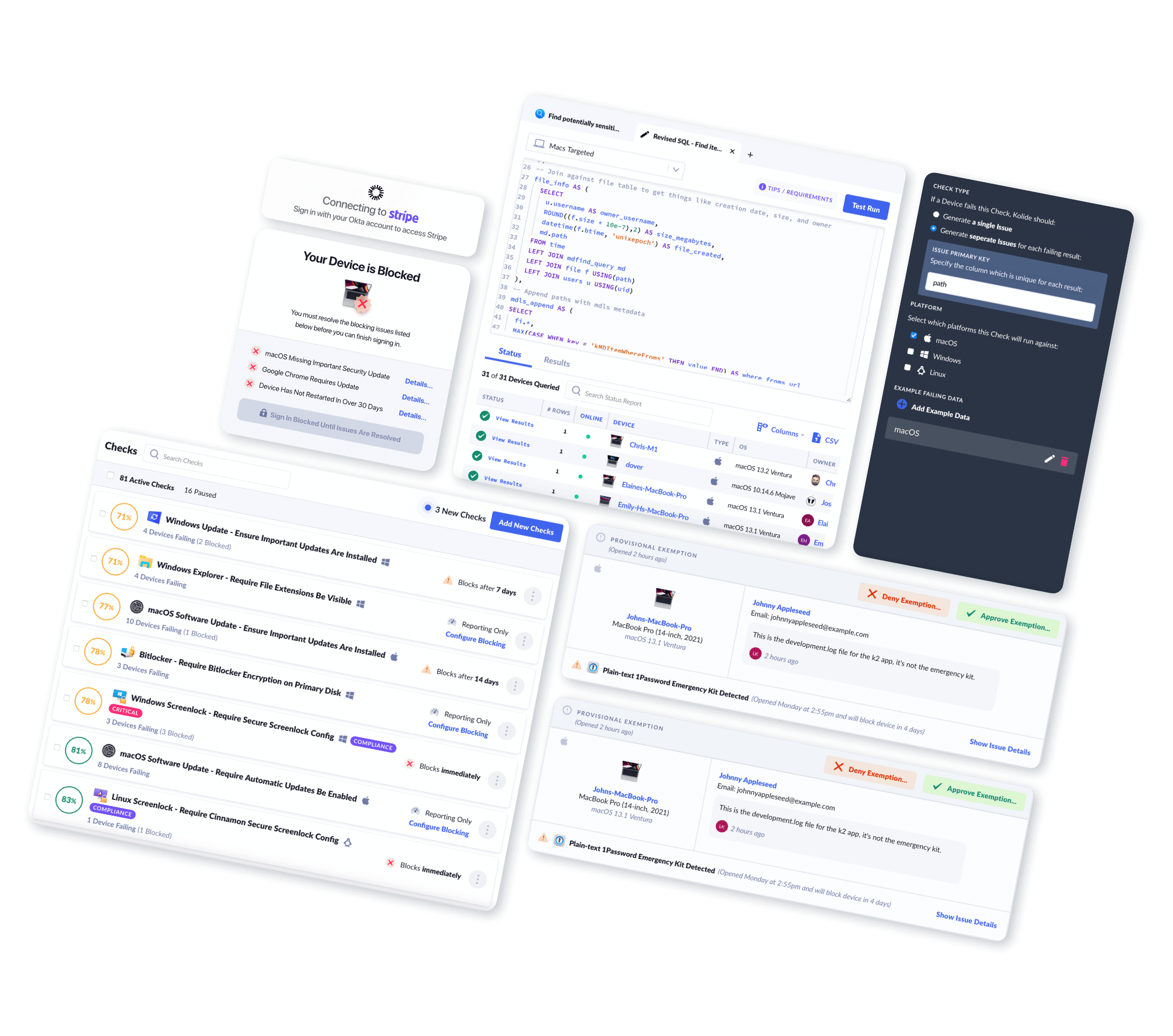
Using Kolide, you can easily view and query Mac SIP Settings across your fleet.
Introduction
SIP stands for System Integrity Protection. Apple's support site provides the following description...
System Integrity Protection is a security technology (macOS 10.11+) designed to help prevent potentially malicious software from modifying protected files and folders on your Mac. System Integrity Protection restricts the root user account and limits the actions that the root user can perform on protected parts of the Mac operating system.
System Integrity Protection also helps prevent software from selecting a startup disk. To select a startup disk, choose System Preferences from the Apple menu, then click Startup Disk. Or hold down the Option key while you restart, then choose from the list of startup disks.
For more information, please refer to the official Apple Support documentation: About System Integrity Protection on your Mac
What Mac SIP Setting Data Can Kolide Collect?
Kolide's endpoint agent bundles in osquery to efficiently collect Mac SIP Settings from Macs in your fleet. Once collected, Kolide will parse, clean up, and centrally store this data in Inventory for your team to view, query, or export via API.
Kolide meticulously documents every piece of data returned so you can understand the results.
Mac SIP Settings Schema
| Column | Type | Description | |
|---|---|---|---|
| id | Primary Key |
Unique identifier for the object |
|
| device_id | Foreign Key |
Device associated with the entry |
|
| device_name | Text |
Display name of the device associated with the entry |
|
| config_flag | Text |
The label of the configuration flag (ex: |
|
| enabled | Boolean |
|
|
| enabled_nvram | Boolean |
|
|
| collected_at | Timestamp |
Time the row of data was first collected in the database |
|
| updated_at | Timestamp |
Time the row of data was last changed in the database |
|
What Can You Do With This Information?
Kolide enables you to write your own queries against the data the agent collects. This allows you to build your own reports and API endpoints. For example, you can:
SELECT
device_id,
device_name,
hardware,
enabled AS sip_enabled
FROM mac_sip_configs msc
JOIN devices d ON d.id = msc.device_id
WHERE config_flag = 'sip'
AND enabled = 'false';| hardware | device_id | device_name | sip_enabled |
|---|---|---|---|
| MacBook Pro (15-inch, 2018) | 60435 | Ashleys-MacBook-Pro | false |
| iMac Pro (2017) | 34723 | daves-imac | false |
| MacBook Pro (16-inch, 2019) | 136727 | balthazar | false |
| MacBook Pro (15-inch, 2016) | 135231 | carl | false |
| MacBook Pro (13-inch, 2018) | 135887 | Franks-MBP | false |
| MacBook Air (2017) | 135848 | Alicia-Air | false |
Why Should I Collect Mac SIP Settings?
Monitoring the configuration of System Integrity Protection is important as it is a critical security component on macOS devices and should not be disabled outside of extenuating circumstances. Devices that do not have System Integrity Protection properly configured are much more susceptible to potential compromise by malicious software.
End-User Privacy Consideration
Kolide practices Honest Security. We believe that data should be collected from end-user devices transparently and with privacy in mind.
This inventory does not capture any personally identifiable information.
When you use Kolide to list Mac SIP Setting data from end-user devices, Kolide gives the people using those devices insight into exactly what data is collected, the privacy implications, and who on the IT team can see the data. This all happens in our end-user privacy center which can be accessed directly by employees.