How to List XProtect Reports Across All Macs
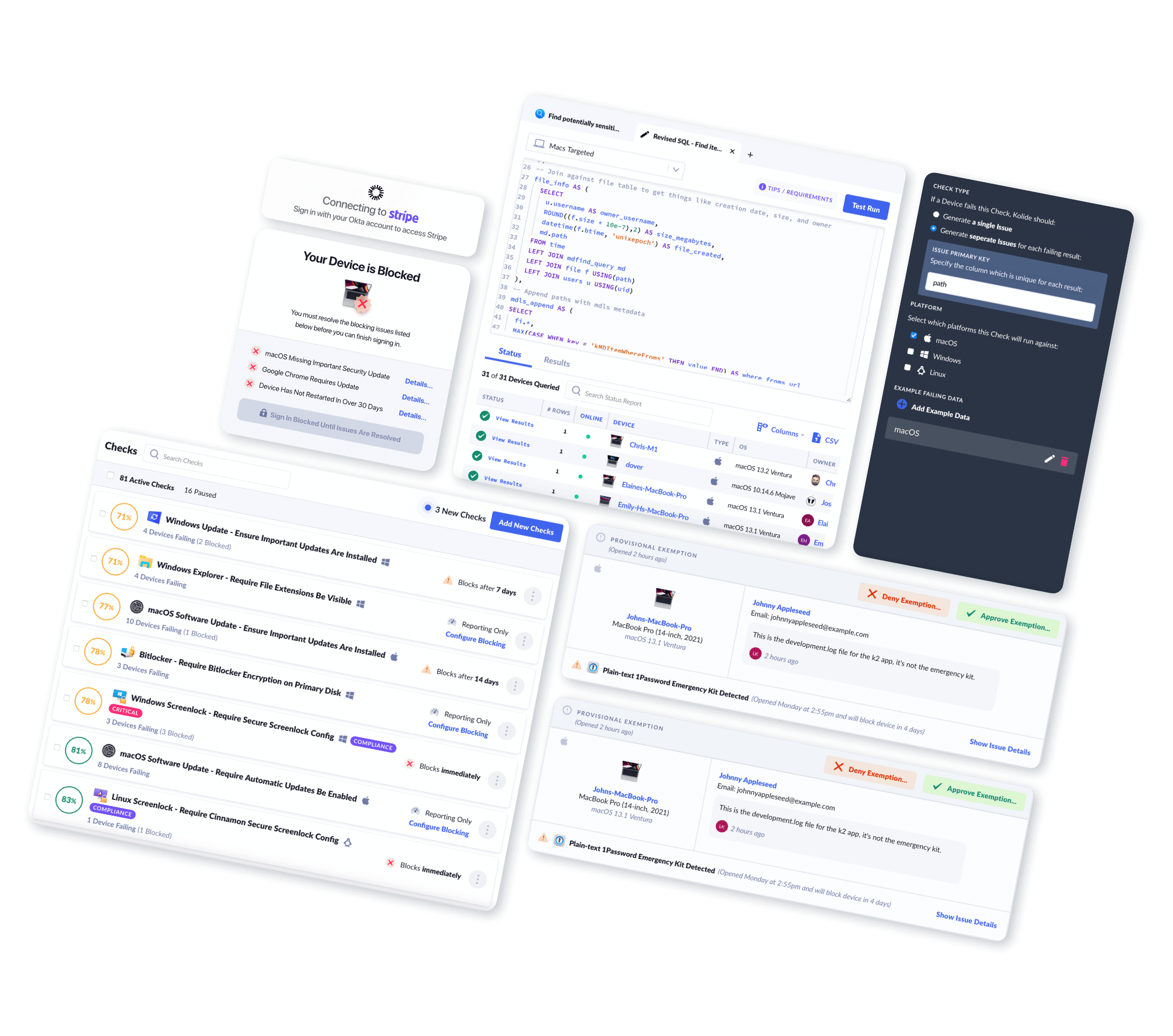
Using Kolide, you can easily view and query Mac XProtect Reports across your fleet.
Introduction
XProtect is a signature-based malware detection utility included and enabled by default in macOS.
XProtect represents one of the 4 core features of macOS malware prevention:
- XProtect (signature-based detection)
- Gatekeeper (unsigned or unidentified software blocking which works with the macOS notarization service)
- Malware Removal Tool or MRT (remediates/removes malware infections)
- System Integrity Protection or SIP (protects certain critical system directories from modification)
XProtect checks for the presence of malware whenever:
- An app is first launched
- An app has been changed (in the file system)
- XProtect signatures are updated
When XProtect detects malware on a device, it prompts the user and then logs
a report to ~/Library/Logs/DiagnosticReports. This inventory captures
information from these reports across devices enrolled in Kolide.
For more information about XProtect please refer to the official Apple Support documentation: Protecting against malware in macOS
What Mac XProtect Report Data Can Kolide Collect?
Kolide's endpoint agent bundles in osquery to efficiently collect Mac XProtect Reports from Macs in your fleet. Once collected, Kolide will parse, clean up, and centrally store this data in Inventory for your team to view, query, or export via API.
Kolide meticulously documents every piece of data returned so you can understand the results.
Mac XProtect Reports Schema
| Column | Type | Description | |
|---|---|---|---|
| id | Primary Key |
Unique identifier for the object |
|
| device_id | Foreign Key |
Device associated with the entry |
|
| device_name | Text |
Display name of the device associated with the entry |
|
| quarantine_bundle_identifier | Text |
This typically represents bundle identifier of the application used to download/obtain the malware Note on data collection: This value is |
|
| quarantine_data_url | Text |
This typically represents the precise URL where the user obtained the malicious file Note on data collection: This value is |
|
| quarantine_origin_url | Text |
This typically represents the URL the browser was displaying before it initaited a download of the malicious file (ex: The user clicked a link on this page which resulted in the browser downloading the malicious file) Note on data collection: This value is |
|
| quaratined_at | Timestamp |
The time the malware's quarantine bit was set by Gatekeeper. This is often analogous to when the file was downloaded or extracted from an archive. |
|
| reported_at | Timestamp |
The time the user opted to generate the diagnostic report which serves as the source of the truth for all the information in this table. This is often very close to the time when the user executed the malware and dismissed any subsequent alert presented by macOS. |
|
| signature_name | Text |
The name of signature that matched ex: Note on data collection: Apple often uses non-standard and purposefully obfuscated names to describe the malware detected by XProtect. The names listed here may not be cross-referenceable to known malware families (by design) |
|
| user_action | Enum::Text |
The action the user performed when they were told by macOS that the file they ran was malicious. Can be one of the following:
|
|
| collected_at | Timestamp |
Time the row of data was first collected in the database |
|
| updated_at | Timestamp |
Time the row of data was last changed in the database |
|
Why Should I Collect Mac XProtect Reports?
IT & Security administrators may review this information to discover confirmed malware that may have been downloaded and executed on a device.
End-User Privacy Consideration
Kolide practices Honest Security. We believe that data should be collected from end-user devices transparently and with privacy in mind.
In certain situations, these XProtect reports may contain the original name of the file as it was downloaded from a website, the name of the web browser used to download the file, and the precise URL the file was obtained from.
This data is only captured by Kolide if the user opts to share the report with Apple.
When you use Kolide to list Mac XProtect Report data from end-user devices, Kolide gives the people using those devices insight into exactly what data is collected, the privacy implications, and who on the IT team can see the data. This all happens in our end-user privacy center which can be accessed directly by employees.