How to List Profiles Across All Macs
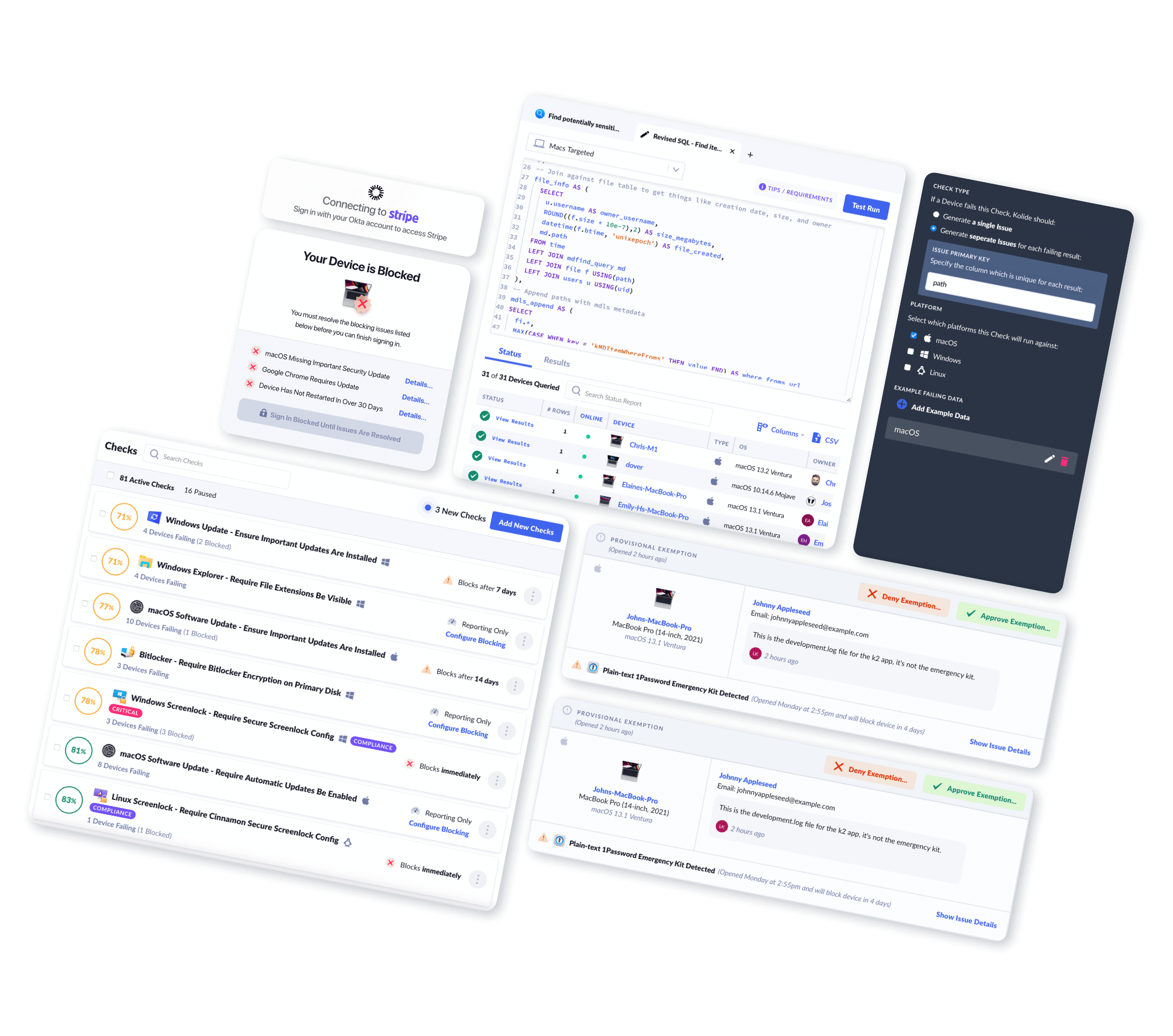
Using Kolide, you can easily view and query Mac Profiles across your fleet.
Introduction
Apple utilizes files called MobileConfig Profiles to facilitate device management and configuration. These profiles can do things such as enroll a device in a Mobile Device Management (MDM) provider, or remotely configure System Preferences.
Configuration profiles let you standardize settings for Mac computers. For example, an administrator can set up profiles that contain settings for a user’s Mail account, Wi-Fi settings, VPN settings, and more.
These installed profiles can be installed in an à la carte manner with separate profiles for each configured setting, or in a broader all-encompassing manner where a single profile configures multiple items at once. These Profiles can be reviewed and managed in the Profiles preference pane of your device.
For more information about Profiles please refer to the official Apple Support documentation: Use configuration profiles to standardize settings on Mac computers
What Mac Profile Data Can Kolide Collect?
Kolide's endpoint agent bundles in osquery to efficiently collect Mac Profiles from Macs in your fleet. Once collected, Kolide will parse, clean up, and centrally store this data in Inventory for your team to view, query, or export via API.
Kolide meticulously documents every piece of data returned so you can understand the results.
Mac Profiles Schema
| Column | Type | Description | |
|---|---|---|---|
| id | Primary Key |
Unique identifier for the object |
|
| device_id | Foreign Key |
Device associated with the entry |
|
| device_name | Text |
Display name of the device associated with the entry |
|
| description | Text |
The value of the |
|
| identifier | Text |
The value of the |
|
| installed_at | Timestamp |
The time the profile was installed |
|
| name | Text |
The |
|
| removal_disallowed | Boolean |
|
|
| uuid | Text |
The value of the |
|
| verification_state | Enum::Text |
The state of the signature (if any) of the installed profile Can be one of the following:
|
|
| version | Text |
The value of the |
|
| collected_at | Timestamp |
Time the row of data was first collected in the database |
|
| updated_at | Timestamp |
Time the row of data was last changed in the database |
|
What Can You Do With This Information?
Kolide enables you to write your own queries against the data the agent collects. This allows you to build your own reports and API endpoints. For example, you can:
SELECT
mac_profiles.device_name,
mac_profiles.name AS profile_name,
mac_profiles.verification_state,
mac_profiles.installed_at
FROM mac_profiles
WHERE mac_profiles.verification_state != 'verified'| device_name | installed_at | profile_name | verification_state |
|---|---|---|---|
| Jasons-MacBook-Pro | 2022-06-26T18:28:21.000Z | Enable Firewall | unsigned |
SELECT
mac_profiles.name AS profile_name,
mac_profiles.description,
mac_profiles.installed_at
FROM mac_profiles
WHERE mac_profiles.removal_disallowed = false;| description | installed_at | profile_name |
|---|---|---|
| Enable Firewall and ensuring logging/stealth mode is also enabled | 2022-06-26T18:28:21.000Z | Enable Firewall |
SELECT
mac_profiles.name AS profile_name,
mac_profiles.description,
mac_profiles.installed_at
FROM mac_profiles
WHERE mac_profiles.uuid = '476DA8E1-8450-4375-A8C0-37232350AC54';| description | installed_at | profile_name |
|---|---|---|
| Disables just the Sharing pane in System Preferences | 2022-06-26T19:03:19.000Z | Disable Sharing |
Why Should I Collect Mac Profiles?
Profiles are an important part of Mac management and information about them can be utilized by your administrator for a variety of purposes including:
- Verifying that your device is enrolled in your organization's Mobile Device Management (MDM) program.
- Verifying the desired configuration of your device such as adherence to a required password policy, or the configuration of your screen-lock settings.
- Reviewing and auditing installed profiles to ensure that potential malicious profiles are not installed on your device.
End-User Privacy Consideration
Kolide practices Honest Security. We believe that data should be collected from end-user devices transparently and with privacy in mind.
Installed profiles do not contain details about the payload (the individual settings being configured), and as such, are unlikely to contain personally identifiable information. These payloads are however available in the Managed Policies inventory, and could conceivably contain details such as your work email address (if an administrator used profiles to configure your Mail client).
Installed profiles could possibly contain identifiable information about you or your device if an administrator named the Profile in an identifying way, for example: Jenny-Slates-Screenlock-Settings however in practice, this is unlikely.
When you use Kolide to list Mac Profile data from end-user devices, Kolide gives the people using those devices insight into exactly what data is collected, the privacy implications, and who on the IT team can see the data. This all happens in our end-user privacy center which can be accessed directly by employees.